Meet the Scientists on the Frontlines of Protecting Humanity from a Man-Made Pathogen

From left: Jean Peccoud, Randall Murch, and Neeraj Rao.
Jean Peccoud wasn't expecting an email from the FBI. He definitely wasn't expecting the agency to invite him to a meeting. "My reaction was, 'What did I do wrong to be on the FBI watch list?'" he recalls.
You use those blueprints for white-hat research—which is, indeed, why the open blueprints exist—or you can do the same for a black-hat attack.
He didn't know what the feds could possibly want from him. "I was mostly scared at this point," he says. "I was deeply disturbed by the whole thing."
But he decided to go anyway, and when he traveled to San Francisco for the 2008 gathering, the reason for the e-vite became clear: The FBI was reaching out to researchers like him—scientists interested in synthetic biology—in anticipation of the potential nefarious uses of this technology. "The whole purpose of the meeting was, 'Let's start talking to each other before we actually need to talk to each other,'" says Peccoud, now a professor of chemical and biological engineering at Colorado State University. "'And let's make sure next time you get an email from the FBI, you don't freak out."
Synthetic biology—which Peccoud defines as "the application of engineering methods to biological systems"—holds great power, and with that (as always) comes great responsibility. When you can synthesize genetic material in a lab, you can create new ways of diagnosing and treating people, and even new food ingredients. But you can also "print" the genetic sequence of a virus or virulent bacterium.
And while it's not easy, it's also not as hard as it could be, in part because dangerous sequences have publicly available blueprints. You use those blueprints for white-hat research—which is, indeed, why the open blueprints exist—or you can do the same for a black-hat attack. You could synthesize a dangerous pathogen's code on purpose, or you could unwittingly do so because someone tampered with your digital instructions. Ordering synthetic genes for viral sequences, says Peccoud, would likely be more difficult today than it was a decade ago.
"There is more awareness of the industry, and they are taking this more seriously," he says. "There is no specific regulation, though."
Trying to lock down the interconnected machines that enable synthetic biology, secure its lab processes, and keep dangerous pathogens out of the hands of bad actors is part of a relatively new field: cyberbiosecurity, whose name Peccoud and colleagues introduced in a 2018 paper.
Biological threats feel especially acute right now, during the ongoing pandemic. COVID-19 is a natural pathogen -- not one engineered in a lab. But future outbreaks could start from a bug nature didn't build, if the wrong people get ahold of the right genetic sequences, and put them in the right sequence. Securing the equipment and processes that make synthetic biology possible -- so that doesn't happen -- is part of why the field of cyberbiosecurity was born.
The Origin Story
It is perhaps no coincidence that the FBI pinged Peccoud when it did: soon after a journalist ordered a sequence of smallpox DNA and wrote, for The Guardian, about how easy it was. "That was not good press for anybody," says Peccoud. Previously, in 2002, the Pentagon had funded SUNY Stonybrook researchers to try something similar: They ordered bits of polio DNA piecemeal and, over the course of three years, strung them together.
Although many years have passed since those early gotchas, the current patchwork of regulations still wouldn't necessarily prevent someone from pulling similar tricks now, and the technological systems that synthetic biology runs on are more intertwined — and so perhaps more hackable — than ever. Researchers like Peccoud are working to bring awareness to those potential problems, to promote accountability, and to provide early-detection tools that would catch the whiff of a rotten act before it became one.
Peccoud notes that if someone wants to get access to a specific pathogen, it is probably easier to collect it from the environment or take it from a biodefense lab than to whip it up synthetically. "However, people could use genetic databases to design a system that combines different genes in a way that would make them dangerous together without each of the components being dangerous on its own," he says. "This would be much more difficult to detect."
After his meeting with the FBI, Peccoud grew more interested in these sorts of security questions. So he was paying attention when, in 2010, the Department of Health and Human Services — now helping manage the response to COVID-19 — created guidance for how to screen synthetic biology orders, to make sure suppliers didn't accidentally send bad actors the sequences that make up bad genomes.
Guidance is nice, Peccoud thought, but it's just words. He wanted to turn those words into action: into a computer program. "I didn't know if it was something you can run on a desktop or if you need a supercomputer to run it," he says. So, one summer, he tasked a team of student researchers with poring over the sentences and turning them into scripts. "I let the FBI know," he says, having both learned his lesson and wanting to get in on the game.
Peccoud later joined forces with Randall Murch, a former FBI agent and current Virginia Tech professor, and a team of colleagues from both Virginia Tech and the University of Nebraska-Lincoln, on a prototype project for the Department of Defense. They went into a lab at the University of Nebraska at Lincoln and assessed all its cyberbio-vulnerabilities. The lab develops and produces prototype vaccines, therapeutics, and prophylactic components — exactly the kind of place that you always, and especially right now, want to keep secure.
"We were creating wiki of all these nasty things."
The team found dozens of Achilles' heels, and put them in a private report. Not long after that project, the two and their colleagues wrote the paper that first used the term "cyberbiosecurity." A second paper, led by Murch, came out five months later and provided a proposed definition and more comprehensive perspective on cyberbiosecurity. But although it's now a buzzword, it's the definition, not the jargon, that matters. "Frankly, I don't really care if they call it cyberbiosecurity," says Murch. Call it what you want: Just pay attention to its tenets.
A Database of Scary Sequences
Peccoud and Murch, of course, aren't the only ones working to screen sequences and secure devices. At the nonprofit Battelle Memorial Institute in Columbus, Ohio, for instance, scientists are working on solutions that balance the openness inherent to science and the closure that can stop bad stuff. "There's a challenge there that you want to enable research but you want to make sure that what people are ordering is safe," says the organization's Neeraj Rao.
Rao can't talk about the work Battelle does for the spy agency IARPA, the Intelligence Advanced Research Projects Activity, on a project called Fun GCAT, which aims to use computational tools to deep-screen gene-sequence orders to see if they pose a threat. It can, though, talk about a twin-type internal project: ThreatSEQ (pronounced, of course, "threat seek").
The project started when "a government customer" (as usual, no one will say which) asked Battelle to curate a list of dangerous toxins and pathogens, and their genetic sequences. The researchers even started tagging sequences according to their function — like whether a particular sequence is involved in a germ's virulence or toxicity. That helps if someone is trying to use synthetic biology not to gin up a yawn-inducing old bug but to engineer a totally new one. "How do you essentially predict what the function of a novel sequence is?" says Rao. You look at what other, similar bits of code do.
"We were creating wiki of all these nasty things," says Rao. As they were working, they realized that DNA manufacturers could potentially scan in sequences that people ordered, run them against the database, and see if anything scary matched up. Kind of like that plagiarism software your college professors used.
Battelle began offering their screening capability, as ThreatSEQ. When customers -- like, currently, Twist Bioscience -- throw their sequences in, and get a report back, the manufacturers make the final decision about whether to fulfill a flagged order — whether, in the analogy, to give an F for plagiarism. After all, legitimate researchers do legitimately need to have DNA from legitimately bad organisms.
"Maybe it's the CDC," says Rao. "If things check out, oftentimes [the manufacturers] will fulfill the order." If it's your aggrieved uncle seeking the virulent pathogen, maybe not. But ultimately, no one is stopping the manufacturers from doing so.
Beyond that kind of tampering, though, cyberbiosecurity also includes keeping a lockdown on the machines that make the genetic sequences. "Somebody now doesn't need physical access to infrastructure to tamper with it," says Rao. So it needs the same cyber protections as other internet-connected devices.
Scientists are also now using DNA to store data — encoding information in its bases, rather than into a hard drive. To download the data, you sequence the DNA and read it back into a computer. But if you think like a bad guy, you'd realize that a bad guy could then, for instance, insert a computer virus into the genetic code, and when the researcher went to nab her data, her desktop would crash or infect the others on the network.
Something like that actually happened in 2017 at the USENIX security symposium, an annual programming conference: Researchers from the University of Washington encoded malware into DNA, and when the gene sequencer assembled the DNA, it corrupted the sequencer's software, then the computer that controlled it.
"This vulnerability could be just the opening an adversary needs to compromise an organization's systems," Inspirion Biosciences' J. Craig Reed and Nicolas Dunaway wrote in a paper for Frontiers in Bioengineering and Biotechnology, included in an e-book that Murch edited called Mapping the Cyberbiosecurity Enterprise.
Where We Go From Here
So what to do about all this? That's hard to say, in part because we don't know how big a current problem any of it poses. As noted in Mapping the Cyberbiosecurity Enterprise, "Information about private sector infrastructure vulnerabilities or data breaches is protected from public release by the Protected Critical Infrastructure Information (PCII) Program," if the privateers share the information with the government. "Government sector vulnerabilities or data breaches," meanwhile, "are rarely shared with the public."
"What I think is encouraging right now is the fact that we're even having this discussion."
The regulations that could rein in problems aren't as robust as many would like them to be, and much good behavior is technically voluntary — although guidelines and best practices do exist from organizations like the International Gene Synthesis Consortium and the National Institute of Standards and Technology.
Rao thinks it would be smart if grant-giving agencies like the National Institutes of Health and the National Science Foundation required any scientists who took their money to work with manufacturing companies that screen sequences. But he also still thinks we're on our way to being ahead of the curve, in terms of preventing print-your-own bioproblems: "What I think is encouraging right now is the fact that we're even having this discussion," says Rao.
Peccoud, for his part, has worked to keep such conversations going, including by doing training for the FBI and planning a workshop for students in which they imagine and work to guard against the malicious use of their research. But actually, Peccoud believes that human error, flawed lab processes, and mislabeled samples might be bigger threats than the outside ones. "Way too often, I think that people think of security as, 'Oh, there is a bad guy going after me,' and the main thing you should be worried about is yourself and errors," he says.
Murch thinks we're only at the beginning of understanding where our weak points are, and how many times they've been bruised. Decreasing those contusions, though, won't just take more secure systems. "The answer won't be technical only," he says. It'll be social, political, policy-related, and economic — a cultural revolution all its own.
Jamie Rettinger with his now fiance Amie Purnel-Davis, who helped him through the clinical trial.
Jamie Rettinger was still in his thirties when he first noticed a tiny streak of brown running through the thumbnail of his right hand. It slowly grew wider and the skin underneath began to deteriorate before he went to a local dermatologist in 2013. The doctor thought it was a wart and tried scooping it out, treating the affected area for three years before finally removing the nail bed and sending it off to a pathology lab for analysis.
"I have some bad news for you; what we removed was a five-millimeter melanoma, a cancerous tumor that often spreads," Jamie recalls being told on his return visit. "I'd never heard of cancer coming through a thumbnail," he says. None of his doctors had ever mentioned it either. "I just thought I was being treated for a wart." But nothing was healing and it continued to bleed.
A few months later a surgeon amputated the top half of his thumb. Lymph node biopsy tested negative for spread of the cancer and when the bandages finally came off, Jamie thought his medical issues were resolved.
Melanoma is the deadliest form of skin cancer. About 85,000 people are diagnosed with it each year in the U.S. and more than 8,000 die of the cancer when it spreads to other parts of the body, according to the Centers for Disease Control and Prevention (CDC).
There are two peaks in diagnosis of melanoma; one is in younger women ages 30-40 and often is tied to past use of tanning beds; the second is older men 60+ and is related to outdoor activity from farming to sports. Light-skinned people have a twenty-times greater risk of melanoma than do people with dark skin.
"When I graduated from medical school, in 2005, melanoma was a death sentence" --Diwakar Davar.
Jamie had a follow up PET scan about six months after his surgery. A suspicious spot on his lung led to a biopsy that came back positive for melanoma. The cancer had spread. Treatment with a monoclonal antibody (nivolumab/Opdivo®) didn't prove effective and he was referred to the UPMC Hillman Cancer Center in Pittsburgh, a four-hour drive from his home in western Ohio.
An alternative monoclonal antibody treatment brought on such bad side effects, diarrhea as often as 15 times a day, that it took more than a week of hospitalization to stabilize his condition. The only options left were experimental approaches in clinical trials.
Early research
"When I graduated from medical school, in 2005, melanoma was a death sentence" with a cure rate in the single digits, says Diwakar Davar, 39, an oncologist at UPMC Hillman Cancer Center who specializes in skin cancer. That began to change in 2010 with introduction of the first immunotherapies, monoclonal antibodies, to treat cancer. The antibodies attach to PD-1, a receptor on the surface of T cells of the immune system and on cancer cells. Antibody treatment boosted the melanoma cure rate to about 30 percent. The search was on to understand why some people responded to these drugs and others did not.
At the same time, there was a growing understanding of the role that bacteria in the gut, the gut microbiome, plays in helping to train and maintain the function of the body's various immune cells. Perhaps the bacteria also plays a role in shaping the immune response to cancer therapy.
One clue came from genetically identical mice. Animals ordered from different suppliers sometimes responded differently to the experiments being performed. That difference was traced to different compositions of their gut microbiome; transferring the microbiome from one animal to another in a process known as fecal transplant (FMT) could change their responses to disease or treatment.
When researchers looked at humans, they found that the patients who responded well to immunotherapies had a gut microbiome that looked like healthy normal folks, but patients who didn't respond had missing or reduced strains of bacteria.
Davar and his team knew that FMT had a very successful cure rate in treating the gut dysbiosis of Clostridioides difficile, a persistant intestinal infection, and they wondered if a fecal transplant from a patient who had responded well to cancer immunotherapy treatment might improve the cure rate of patients who did not originally respond to immunotherapies for melanoma.
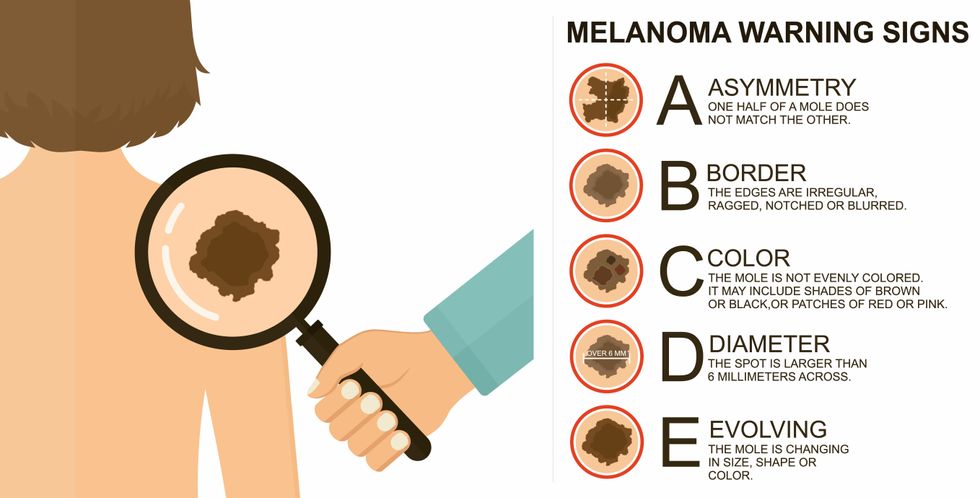
The ABCDE of melanoma detection
Adobe Stock
Clinical trial
"It was pretty weird, I was totally blasted away. Who had thought of this?" Jamie first thought when the hypothesis was explained to him. But Davar's explanation that the procedure might restore some of the beneficial bacterial his gut was lacking, convinced him to try. He quickly signed on in October 2018 to be the first person in the clinical trial.
Fecal donations go through the same safety procedures of screening for and inactivating diseases that are used in processing blood donations to make them safe for transfusion. The procedure itself uses a standard hollow colonoscope designed to screen for colon cancer and remove polyps. The transplant is inserted through the center of the flexible tube.
Most patients are sedated for procedures that use a colonoscope but Jamie doesn't respond to those drugs: "You can't knock me out. I was watching them on the TV going up my own butt. It was kind of unreal at that point," he says. "There were about twelve people in there watching because no one had seen this done before."
A test two weeks after the procedure showed that the FMT had engrafted and the once-missing bacteria were thriving in his gut. More importantly, his body was responding to another monoclonal antibody (pembrolizumab/Keytruda®) and signs of melanoma began to shrink. Every three months he made the four-hour drive from home to Pittsburgh for six rounds of treatment with the antibody drug.
"We were very, very lucky that the first patient had a great response," says Davar. "It allowed us to believe that even though we failed with the next six, we were on the right track. We just needed to tweak the [fecal] cocktail a little better" and enroll patients in the study who had less aggressive tumor growth and were likely to live long enough to complete the extensive rounds of therapy. Six of 15 patients responded positively in the pilot clinical trial that was published in the journal Science.
Davar believes they are beginning to understand the biological mechanisms of why some patients initially do not respond to immunotherapy but later can with a FMT. It is tied to the background level of inflammation produced by the interaction between the microbiome and the immune system. That paper is not yet published.
Surviving cancer
It has been almost a year since the last in his series of cancer treatments and Jamie has no measurable disease. He is cautiously optimistic that his cancer is not simply in remission but is gone for good. "I'm still scared every time I get my scans, because you don't know whether it is going to come back or not. And to realize that it is something that is totally out of my control."
"It was hard for me to regain trust" after being misdiagnosed and mistreated by several doctors he says. But his experience at Hillman helped to restore that trust "because they were interested in me, not just fixing the problem."
He is grateful for the support provided by family and friends over the last eight years. After a pause and a sigh, the ruggedly built 47-year-old says, "If everyone else was dead in my family, I probably wouldn't have been able to do it."
"I never hesitated to ask a question and I never hesitated to get a second opinion." But Jamie acknowledges the experience has made him more aware of the need for regular preventive medical care and a primary care physician. That person might have caught his melanoma at an earlier stage when it was easier to treat.
Davar continues to work on clinical studies to optimize this treatment approach. Perhaps down the road, screening the microbiome will be standard for melanoma and other cancers prior to using immunotherapies, and the FMT will be as simple as swallowing a handful of freeze-dried capsules off the shelf rather than through a colonoscopy. Earlier this year, the Food and Drug Administration approved the first oral fecal microbiota product for C. difficile, hopefully paving the way for more.
An older version of this hit article was first published on May 18, 2021
All organisms can repair damaged tissue, but none do it better than salamanders and newts. A surprising area of science could tell us how they manage this feat - and perhaps even help us develop a similar ability.
All organisms have the capacity to repair or regenerate tissue damage. None can do it better than salamanders or newts, which can regenerate an entire severed limb.
That feat has amazed and delighted man from the dawn of time and led to endless attempts to understand how it happens – and whether we can control it for our own purposes. An exciting new clue toward that understanding has come from a surprising source: research on the decline of cells, called cellular senescence.
Senescence is the last stage in the life of a cell. Whereas some cells simply break up or wither and die off, others transition into a zombie-like state where they can no longer divide. In this liminal phase, the cell still pumps out many different molecules that can affect its neighbors and cause low grade inflammation. Senescence is associated with many of the declining biological functions that characterize aging, such as inflammation and genomic instability.
Oddly enough, newts are one of the few species that do not accumulate senescent cells as they age, according to research over several years by Maximina Yun. A research group leader at the Center for Regenerative Therapies Dresden and the Max Planck Institute of Molecular and Cell Biology and Genetics, in Dresden, Germany, Yun discovered that senescent cells were induced at some stages of regeneration of the salamander limb, “and then, as the regeneration progresses, they disappeared, they were eliminated by the immune system,” she says. “They were present at particular times and then they disappeared.”
Senescent cells added to the edges of the wound helped the healthy muscle cells to “dedifferentiate,” essentially turning back the developmental clock of those cells into more primitive states.
Previous research on senescence in aging had suggested, logically enough, that applying those cells to the stump of a newly severed salamander limb would slow or even stop its regeneration. But Yun stood that idea on its head. She theorized that senescent cells might also play a role in newt limb regeneration, and she tested it by both adding and removing senescent cells from her animals. It turned out she was right, as the newt limbs grew back faster than normal when more senescent cells were included.
Senescent cells added to the edges of the wound helped the healthy muscle cells to “dedifferentiate,” essentially turning back the developmental clock of those cells into more primitive states, which could then be turned into progenitors, a cell type in between stem cells and specialized cells, needed to regrow the muscle tissue of the missing limb. “We think that this ability to dedifferentiate is intrinsically a big part of why salamanders can regenerate all these very complex structures, which other organisms cannot,” she explains.
Yun sees regeneration as a two part problem. First, the cells must be able to sense that their neighbors from the lost limb are not there anymore. Second, they need to be able to produce the intermediary progenitors for regeneration, , to form what is missing. “Molecularly, that must be encoded like a 3D map,” she says, otherwise the new tissue might grow back as a blob, or liver, or fin instead of a limb.
Wound healing
Another recent study, this time at the Mayo Clinic, provides evidence supporting the role of senescent cells in regeneration. Looking closely at molecules that send information between cells in the wound of a mouse, the researchers found that senescent cells appeared near the start of the healing process and then disappeared as healing progressed. In contrast, persistent senescent cells were the hallmark of a chronic wound that did not heal properly. The function and significance of senescence cells depended on both the timing and the context of their environment.
The paper suggests that senescent cells are not all the same. That has become clearer as researchers have been able to identify protein markers on the surface of some senescent cells. The patterns of these proteins differ for some senescent cells compared to others. In biology, such physical differences suggest functional differences, so it is becoming increasingly likely there are subsets of senescent cells with differing functions that have not yet been identified.
There are disagreements within the research community as to whether newts have acquired their regenerative capacity through a unique evolutionary change, or if other animals, including humans, retain this capacity buried somewhere in their genes.
Scientists initially thought that senescent cells couldn’t play a role in regeneration because they could no longer reproduce, says Anthony Atala, a practicing surgeon and bioengineer who leads the Wake Forest Institute for Regenerative Medicine in North Carolina. But Yun’s study points in the other direction. “What this paper shows clearly is that these cells have the potential to be involved in tissue regeneration [in newts]. The question becomes, will these cells be able to do the same in humans.”
As our knowledge of senescent cells increases, Atala thinks we need to embrace a new analogy to help understand them: humans in retirement. They “have acquired a lot of wisdom throughout their whole life and they can help younger people and mentor them to grow to their full potential. We're seeing the same thing with these cells,” he says. They are no longer putting energy into their own reproduction, but the signaling molecules they secrete “can help other cells around them to regenerate.”
There are disagreements within the research community as to whether newts have acquired their regenerative capacity through a unique evolutionary change, or if other animals, including humans, retain this capacity buried somewhere in their genes. If so, it seems that our genes are unable to express this ability, perhaps as part of a tradeoff in acquiring other traits. It is a fertile area of research.
Dedifferentiation is likely to become an important process in the field of regenerative medicine. One extreme example: a lab has been able to turn back the clock and reprogram adult male skin cells into female eggs, a potential milestone in reproductive health. It will be more difficult to control just how far back one wishes to go in the cell's dedifferentiation – part way or all the way back into a stem cell – and then direct it down a different developmental pathway. Yun is optimistic we can learn these tricks from newts.
Senolytics
A growing field of research is using drugs called senolytics to remove senescent cells and slow or even reverse disease of aging.
“Senolytics are great, but senolytics target different types of senescence,” Yun says. “If senescent cells have positive effects in the context of regeneration, of wound healing, then maybe at the beginning of the regeneration process, you may not want to take them out for a little while.”
“If you look at pretty much all biological systems, too little or too much of something can be bad, you have to be in that central zone” and at the proper time, says Atala. “That's true for proteins, sugars, and the drugs that you take. I think the same thing is true for these cells. Why would they be different?”
Our growing understanding that senescence is not a single thing but a variety of things likely means that effective senolytic drugs will not resemble a single sledge hammer but more a carefully manipulated scalpel where some types of senescent cells are removed while others are added. Combinations and timing could be crucial, meaning the difference between regenerating healthy tissue, a scar, or worse.

